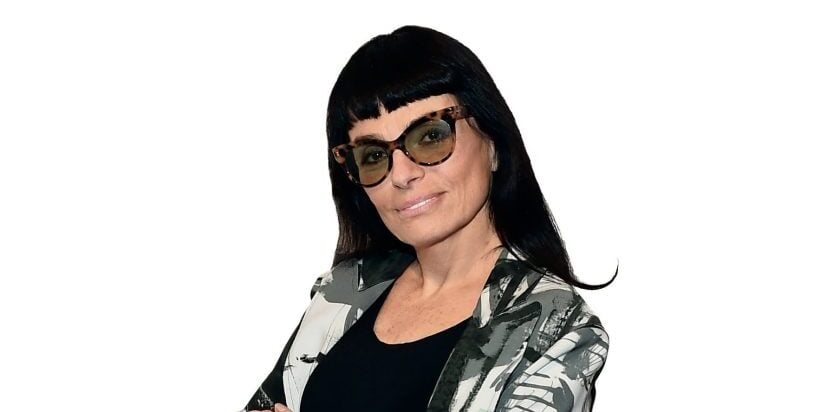
Carson Block is one of the rebels of finance. While working in China in the 2000s, he grew skeptical of the financial status of several prominent Chinese companies, which led him to found the financial research firm Muddy Waters and make several high-profile short-selling plays. Block’s bets generated anger from Chinese authorities and international investors alike—even after they proved to be correct. Recently, Block has been making headlines for his public announcement last August that he shorted the stock of medical device maker St. Jude Medical. The company’s pacemakers and defibrillators, Block warned, are dangerously vulnerable to computer hackers who could, essentially, turn them off. St. Jude, which was in the process of being bought for $25 billion by medical company Abbot Laboratories, promptly filed a lawsuit against Block, which is ongoing.
Worth spoke with Block about the St. Jude short, his own outsider position in the financial world, and why people get so pissed off at short-sellers.
What sparked your interest in cybersecurity?
It stems from when I lived in China from 2005 to 2010, and I saw China become a complete surveillance state. It’s something I was always sensitive to. When we started Muddy Waters [in 2010], I knew I had to get clean computers. We would use burner SIMs and phones in case the government might interfere with us. You’d have to throw them away as soon as you were done.

Let’s talk about St. Jude specifically. How and why did you decide to short the stock?
I never considered a cyber-security short until a [Miami–based] company called Medsec approached me with the idea. I can only do something if there are economics that justify it, but I’ve been very perturbed for a number of years about the lack of awareness or concern regarding cyber security in the U.S. and western countries in general.
What made Medsec come to you?
A guy I knew from when I shorted a Chinese company called NQ Mobile started Medsec. I hadn’t seen him in a few years, but he pinged me saying he would be in San Francisco and that he’d like to catch up. I sat down with him, and he told me he had founded this firm called Medsec that was looking for security vulnerabilities in medical devices. He asked if anyone had a thesis on a medical device that provided life-saving therapy that was ridiculously easy to hack— which to me translated to gross negligence in the design. He asked if I was interested, and I was.
Wouldn’t it be the responsible thing for a medical security company to alert St. Jude of any vulnerabilities? After all, there are lives at stake.
That’s a concept called responsible disclosure. And St. Jude was put on notice of vulnerabilities in 2014, when it was reported that the Department of Homeland Security had investigated [the possibility that St. Jude medical devices could be compromised]. One well-known researcher by the name Barnaby Jack—these people don’t like the term “hacker,” but that would be the common nomenclature—identified these vulnerabilities. My understanding is that he approached St. Jude and basically spurred the DHS investigation. Ultimately, he was unsatisfied because St. Jude had not remediated this, so he announced that he was going to publicly demonstrate this at a conference in Australia. But the night before the presentation, he overdosed and died.

Are you a conspiracy theorist? Were the circumstances suspicious?
(Laughs) No, I don’t think St. Jude killed him.
In theory, how should responsible disclosure work?
Well, under responsible disclosure guidelines, you first give the company an opportunity to remediate. And if they don’t, then you expose the vulnerability. It’s clear that St. Jude didn’t meaningfully improve security after the DHS investigation. And it’s hard to conclude that St. Jude made a good faith to address these issues. We did due diligence on this—one of my in-house analysts was a software developer, and in many cases, we were able to exploit these vulnerabilities in the at-home devices in just 15 to 20 minutes.
OK, let’s talk about the alleged vulnerabilities. What were you looking at, and what did you find?
You’ve got an ecosystem. You have an implantable device, then you have the home devices that they give to everyone and want you to use, and then you’ve got the servers for St. Jude.
So the purpose of the at-home units is that during the night they download the data and send it to servers at St. Jude, which then alert doctors if there’s any issues with battery or heart rhythm. You have physician office programmers, and these programmers have all the commands that you can give to a device. There are two different, relevant devices: pacemakers and defibrillators. Defibs have a command called “Shock on T,” which can induce fibrillation. To test the device, doctors will induce a heart attack to a patient just to make sure the device will do its job. That’s the ecosystem.
Medsec started with an at-home unit. Just by using the home device, they were able to reverse-engineer enough code to deplete the battery—it would take time, but it would happen—and also to crash them. They would become non-communicative and no one would know. That was just by using code that they found in the at-home device.
Through the at-home device, they could access the dial-in number for St. Jude’s server, which Medsec believes is the development server. The big problem is that all of this information—the dial-in number, the password, the SSH keys—were all stored unencrypted on the at-home device. None of this should have been left in unencrypted form on a device that takes so little time and effort to hack. Any network can be penetrated by a sophisticated enough adversary, but leaving network credentials and SSH keys in an easy to access format would obviously make the job of an attacker easier, and the big concern that we had is that a very sophisticated attacker, such as a nation-state or possibly a terrorist group like ISIS, by accessing the network could upload attack code that would be distributed to the at-home devices. From there they could attack the server or the device as the person slept. Pacemakers and defibs worldwide—probably about a million in the world.
When we went out and saw the demo Medsec did on the at-home device, my analyst said to me, “How many people at St. Jude touched these devices, worked on these things over the years, and thought, ‘We’re cutting corners but, oh well, I want to get my bonus so I need to keep things within budget.’’
It reminds me of the Homeland episode [“Broken Hearts”] in which the vice-president is killed by someone who hacks his pacemaker and gives him a heart attack.
It reminded me of 9/11. At the time, a lot infuriated me, but especially the whole “How could we have seen this coming?” argument. But I had read a Tom Clancy novel [1994’s Debt of Honour] with a similar situation—people had imagined this stuff beforehand. So as an intelligence agency, you can’t say you never saw it coming. And the fact that this scenario was in Homeland and the company had left this vulnerability wide open…
Last September, after you published your findings online, St. Jude filed a defamation lawsuit against you, basically accusing you of lying in order to profit off your short. What’s your response?
They had their chance, they didn’t do anything to fix it, so yes, they deserved to be exposed.
Is there a larger cultural problem with cyber security? Despite all the warnings, lots of people still don’t worry about it very much.
Yeah, and I can’t get on the same wavelength with people who don’t seem to care. I have conversations with people who have Alexa or Google Home, and I say, “You have an open mic to the entire world.” And they’re like, “Who cares? I’m not going to say anything embarrassing or incriminating.” Well, are you sure? And even if you don’t, things could be taken out of context or even spliced together.
What are the consequences of that lack of concern about the internet of things?
Regarding Alexa and Google, I think we’re probably headed towards a massive amount of Americans being blackmailed. About IOT generally, it can have profound consequences—these IOT devices could be connected to critical networks like hospitals and infrastructure. The possible bad outcomes are really just limited by one’s imagination. I think it’s highly likely that at some point we are going to have a cyberattack that has catastrophic consequences.
Back when you first started Muddy Waters, some people thought of you as, basically, some punk kid who was in over his head. After the successes you’ve had, are you a statesman now?
(Laughs) It’s all relative. I met with this one fund face-to-face yesterday, a pretty big fund. And the guy I met with was like, “You know, you seem like a pretty smart, nice guy…for a short seller.”
Why is there so much hostility to short-sellers, do you think?
Sometimes the best lessons we learn are painful ones. A lot of enmity came my way from retail investors, and it took me a little while to understand their mentality. My first job out of college, I was working as a banker in Los Angeles, and I hated it. I’d buy a lottery ticket every day and fantasize about what expletives I’d use to go in and quit my job if I won. A lot of these guys focus on micro caps because there’s some sort of emotional or financial hole in their life, and I was taking their tickets and ripping them up.
So you’re a slap in the face to people who think they’re going to hit it big with some hot stock?
Right after I moved back from China, I had an experience that was illustrative of this mindset. I was at a holiday party, and I wasn’t telling people what I did. I was introduced to this one guy, and knowing that I’d just moved back from China, he was interested in whether I invested in Chinese companies. I told him I was known for shorting a couple of these companies, and he asked if I was “that Muddy Waters guy.” I said yeah, and he asked if I had heard of China MediaExpress, a company which I knew was a fraud. I couldn’t disclose that we were working on a report about the company, so I told him that it had serious problems and that I’d stay away from it. We published that report a couple days later, and a week later he called and asked if it was for real because he wanted to invest now that the stock was down. He said he was thinking of going “all in.”
It’s almost as if the stock market were like Las Vegas—you’re a better, more alive person if you take big risks.
When I watched financial television—which I don’t anymore—many of the ads for day-trading platforms revolved around the concept of being a man among boys. Everything played upon male insecurity. That is retail investing culture. If it didn’t work, they’d stop doing it.
What’s the status of the lawsuit?
There hasn’t been much movement in the case. But before we publish, we’re always confident that we’ll get through a suit without losing. We never publish anything that we think may be a close call. It’s just a question of how soon we can get rid of it.
For more information, visit visit muddywatersresearch.com.